2:30 PM on an overcast Tuesday in August. You can smell the earth from the coming monsoon deluge even twelve stories up in our quiet conference room, where, for some reason, the power is flickering. Over the next six hours, we will hack into one of the world’s largest banks. Thrice.
This is a cautionary tale of why you can’t prevent a motivated hacker from ‘getting in’, no matter how much of your cybersecurity budget is spent on sleek blinking boxes and Zegna-clad consultants.
It’s why you never gamble against human resolve and ingenuity, but bet big on smart people consistently making bad decisions. For, as hackers say;
“There is no patch for human stupidity”
The Job
“These guys are no helpless newbies.”
J, one of our red-teamers, takes a long drag from a clove cigarette and watches the rain obscure the distant railway tracks. He’s right. The bank has state of the art security systems, manned by one of the most skilled infosec teams in the business.
The bank hires us to do this breach readiness assessment / red-team /penetration test stuff regularly, but this time the mission is different.
We’re trying to dispel the myth that it is even possible to defend against an initial intrusion. Our success (or failure) will decide how much effort they now put into prevention (locking the door), as opposed to detection and response (spot the burglar early and take them down fast).
Interlude: An Intrusion v/s A Breach
There’s a nuanced difference between an intrusion and a breach, and once you see it, you’ll never interchange the words again.
Most importantly, you can (and will) have intrusions, without necessarily experiencing breaches. How so?
Just like The Simpsons, the wonderful Richard Bejtlich already did it (and put it rather well):
An intrusion is unauthorized access to a computing resource. A breach is the theft, alteration, or destruction of that computing resource, following an intrusion.
One can avoid a breach following an intrusion if the security team can stop the adversary before he accomplishes his mission.
There is no point at which any network is intrusion-proof. It is more likely one could operate a breach-proof network, but that is not completely attainable, either.
Rules of Engagement
Back to the hack.
We must consistently and repeatedly subvert the banks security. It’s Moscow rules: Once is luck, twice is a coincidence, thrice is a pattern.
Oh, and anything is fair game. In fact, we’re expected to play as dirty as possible.
Here are just some of the preventive controls getting in the way:
- Application white-listing
- Internet access only to a pre-approved site list
- Air-gapped admin network (each admin has two physically separate desktops, and uses a KVM to switch between them)
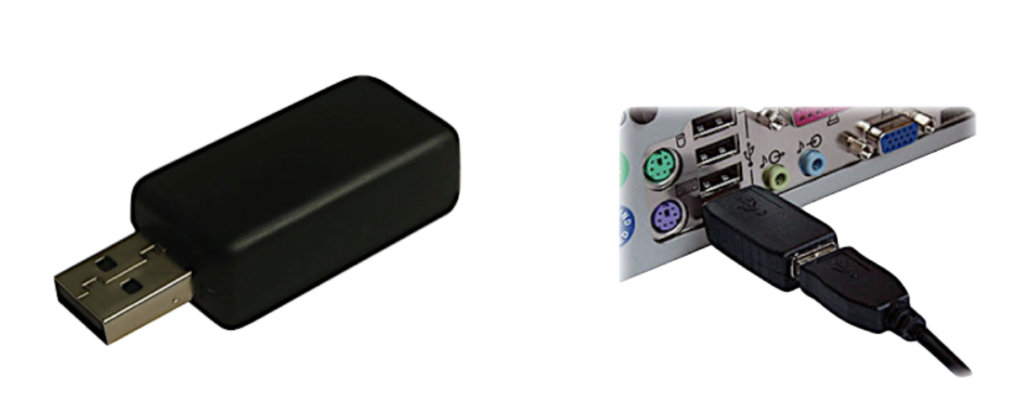
- USB devices totally blocked
- External links in emails quarantined to catch phishing
- Two-factor authentication for all critical servers
- Scary nightclub-bouncer-style physical security
Hack 1 – Cell-phone hacking
Our first target is a small branch. Extensive reconnaissance (a.k.a a couple of phone calls) reveals that they have an on-site IT manager named Todd.
We’re going to hack Todd using a cell-phone…
Roadblock 1:
USB devices are blocked, but we find out that Todd in particular has access to a CD-ROM for some long-forgotten business requirement. Code execution is even easier — We’re going with PowerShell, expecting that the IT manager will be allowed to use it.
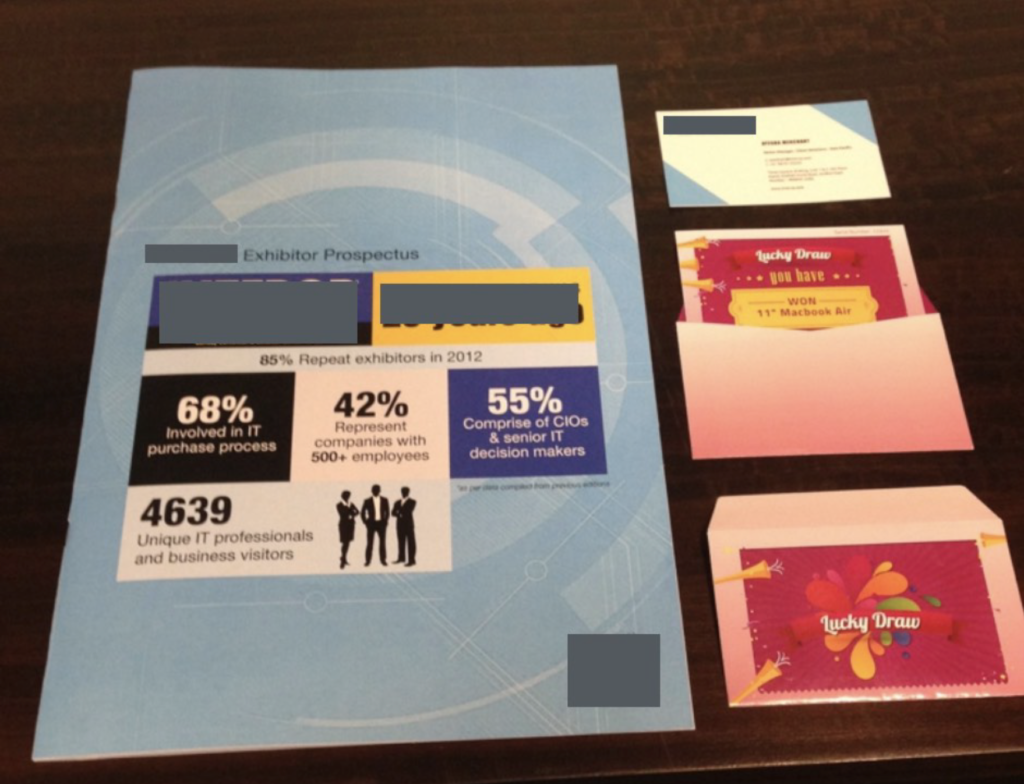
We print up brochures asking Todd to attend an IT event (by invitation only, as these things often claim). We’ve also printed 25 lucky draw scratch cards, but the dice is loaded and the deck is stacked:
Beneath the inviting silver foil, every scratch card has the same prize — an iPhone 7s.
Our forward team, Myra and J, head over with the newly minted material and a CD containing our PowerShell malware. If executed, it will give us external access to the bank from our command and control server. J is wearing a hidden camera.


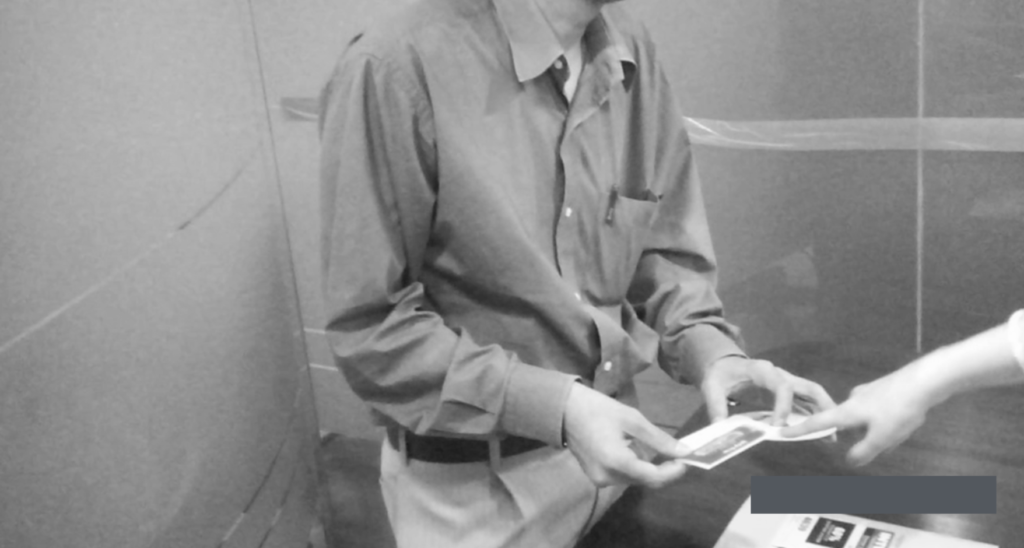
<click> <click>
Roadblock 2:
The bank blocks all sites except for an approved list of categories on their proxy. If our command and control server isn’t in the ‘banking websites’ category, we won’t gain access. Our solution? Ask the proxy vendor nicely. Yes, this worked.
With remote access to their branch network, we move laterally, escalate privileges, and gain access to a bunch of critical servers.
Hack #1 complete.
Hack 2 – Humans are indeed resources for ‘Human Resources’
“There are only two departments nobody messes with — the first is payroll, and the second is H.R.”, Corvus, our finance manager proclaims unsolicited.
Lightbulbs go off at the same time as the power comes back on.
It’s true, our experiments show that employees have an almost Pavlovian response to acquiescing to H.R. queries.
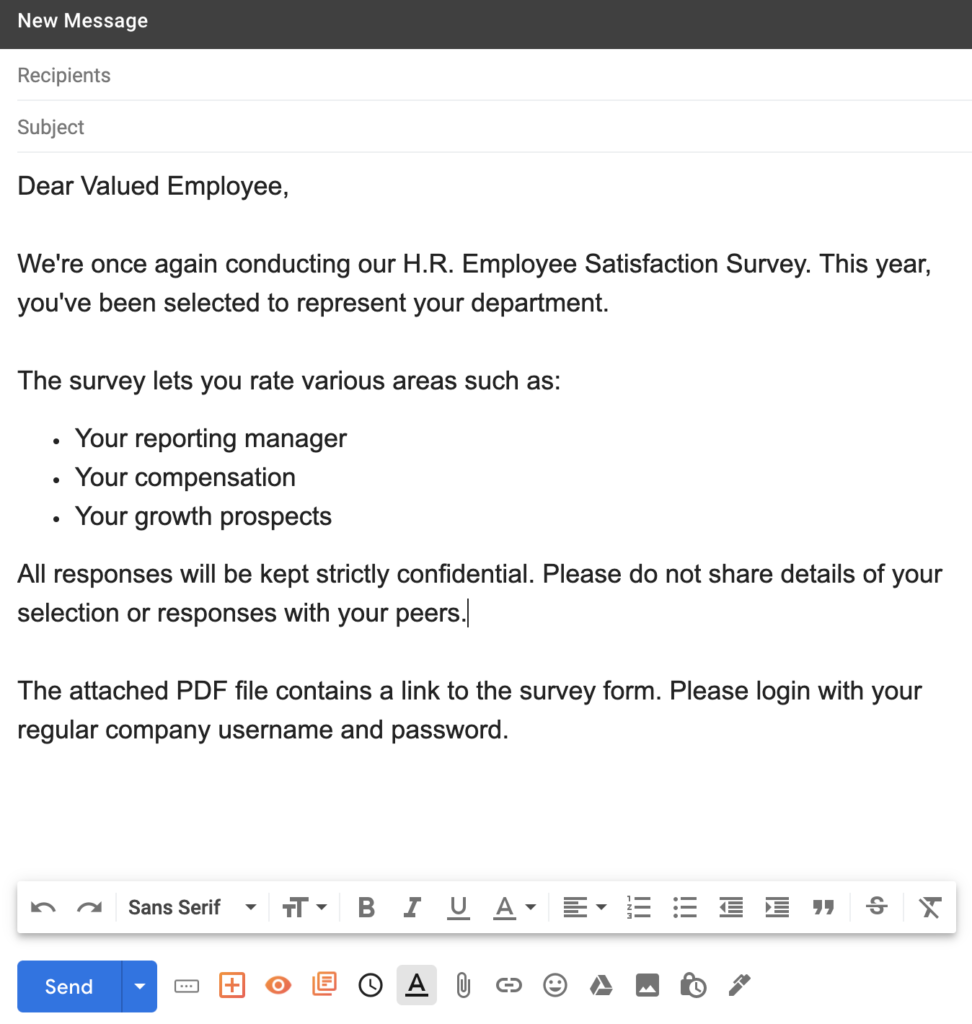
The email went out to a selection of employees on LinkedIn that deal with
ATMs, cardholder data, and transaction processing systems such as SWIFT. We threw in some digital marketing folks, as they’re notoriously click-happy.
Roadblock 3:
The email link scanning and quarantine system wouldn’t allow a link in an email but also wouldn’t care about them inside documents. The PDF link leads to a customized phishing page and an actual survey to submit, because, why not?
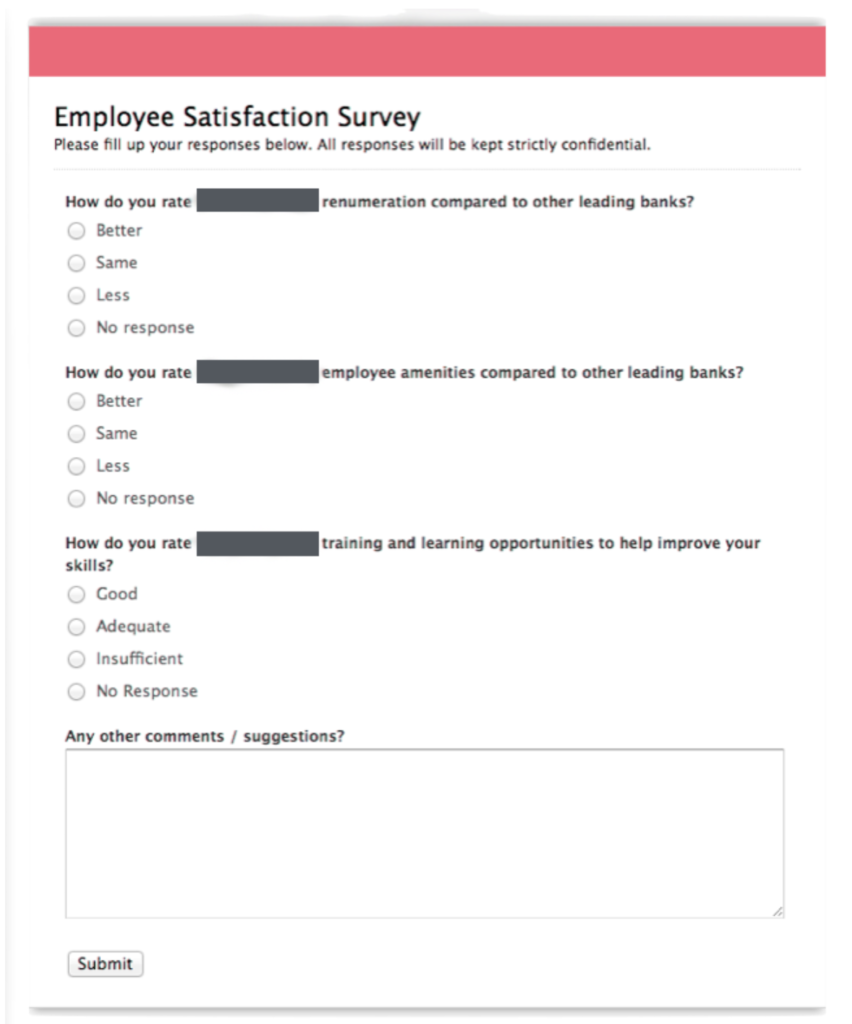
Two hours later we have over 40 phished credentials and an 84% success rate.
Hack #2 complete.
Hack 3 – Burger, fries, and a complimentary keyboard upgrade
The success of the first two hacks has the team getting cocky. Myra is the first to broach the idea of physically getting to the trading floor systems.
Perhaps it’s the cups of coffee, or the desire to get out of the office again.
Why not? The weather’s perfect!
Roadblock 4:
The. Trading. Floor. Where separate lifts are manned by the aforementioned security staff who lift heavy objects for fun. The domain of the traders, with their special orange lanyards, who eat at the more upscale eateries down the street, because well, that’s what traders do.
J’s a hardware guy. The traders have RFID badges. Identifiable orange lanyards that they leave at their tables in the restaurant. 45 minutes and much ProxMox configuration in the back of a car later, we have a clone of one of their RFID cards (HID Prox II).
We’re still not sure it will work though. A guard eyeballs J as he walks toward the door. The guard’s hand moves to his revolver (okay, the gun never happened, but J tells it like that for the ladies). He approaches the RFID scanner.
<blink and beep> We’re in.
J’s got three brand new keyboards under his arm (the nifty ones with LEDs and integrated trackball). He walks into the cabins of three staffers and says;
“Hey I’m from I.T., I’m here to install your keyboard upgrade.”
Each of the keyboards has a Wi-fi keylogger attached to the end. Nobody refuses the upgrade. However, one manager makes J spend half an hour debugging Outlook and yells at him when he can’t fix it. J uses Mutt.
We sit in the parking lot with a wireless antenna, watching them type in trades and send emails full of in-jokes until the sun goes down. It’s still raining.
Hack #3 complete.
The notion that initial intrusions can be reliably prevented is extremely flawed, especially when you don’t know what lengths the attacker will go to win.
This is not to say that we abandon the idea of prevention and leave the doors wide open. Prevention systems can stop a lot of the low hanging fruit — commodity malware, regular phishing, Internet scans. Just don’t expect it to thwart the highly targeted attacks.
The cybersecurity industry is moving towards ‘assume breach’, shifting
resources from ‘prevent’, to ‘detect and respond’, however it’s moving way too slowly.
Far too many defenders still don’t viscerally understand that this is the way it should be. Worse, this paradigm is often not communicated or well-received by the board, leading to mismatched expectations when intrusions inevitably occur.
If this sounds familiar to you, help move things along by sharing this story, as well as your own.
It’s about time we got out from under this cloud.
- Detect zero-days, APTs, and insider threats
- 10x the detection capabilities with 1/2 the team
- Get started in minutes, fully functional in hours
