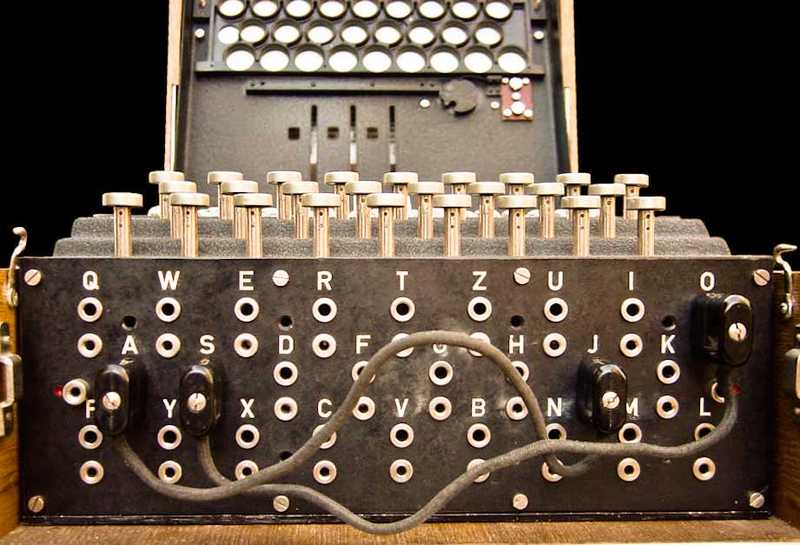
Conceptually, deception is an incredibly intuitive approach to cybersecurity. The parallels between deception in the real-world, and deception in cyberspace are clear and easy to understand. However, in the digital battlefield it’s far more nuanced — it’s easy to do it badly, and far harder to get it right. Which makes it rather similar to a more traditional security practice — cryptography.
Cryptographers are familiar with a well-known axiom called Kerckhoff’s principle, which states:
A cryptosystem should be secure even if everything about the system, except the key, is public knowledge.
This was famously paraphrased by Claude Shannon in what is known as Shannon’s Maxim:
“The enemy knows the system“, i.e., “one ought to design systems under the assumption that the enemy will immediately gain full familiarity with them“
The applicability to deception is immediately apparent. It should remain effective, even when an attacker:
- Knows that deception technology is deployed
- Knows the full capabilities of the specific solution
- Intuitively understands where the decoys may be deployed (ATM, SWIFT, SCADA, IoT etc.)
However, the exact map of the minefield — the specific placement of decoys, their running services, and their content is not known. This deception map is the equivalent of the secret key in a crypto-system. As long as the map is not known to the attacker, the illusion should still remain extremely effective, despite the attacker having complete visibility into the rest of the system.
At Smokescreen, we are laser focused on making sure deception is ‘done right’ — with the necessary rigour and formal reasoning to hold up in real-world conditions. How do we do this? Our depth of experience in related cybersecurity disciplines is our secret weapon. We apply hard earned knowledge from red-teaming, asymmetric thinking, threat hunting, cryptography and incident response to build the most formidable and effective deception system available.
Continue Reading
Using deception to shield the insurance sector
Insurance companies are under siege from cyberattacks. We take a look at some of the key pieces of an insurer’s infrastructure the adversaries target and how you can use deception to build active defenses.By Sudarshan Pisupati7 Ways to Fail At Implementing Deception Technology
Since there’s precious little information on how security teams can make deception implementations successful (some folks like to keep it a secret), there’s plenty that can go wrong. Here are 7 ways to completely botch your deployment of deception technology.By Smokescreen Team10 Questions To Ask Deception Technology Vendors
Deception technology is a major buzzword today. In order for you to cut through the marketing hype, here’s a set of evaluation questions that will help you better understand disparate deception offerings and identify vendors that know what they’re doing.By Smokescreen Team
- Detect zero-days, APTs, and insider threats
- 10x the detection capabilities with 1/2 the team
- Get started in minutes, fully functional in hours